The Blockchain Internet of Things, or BIoT, is the powerful fusion of two transformative technologies. It combines the Internet of Things’ (IoT) vast network of data-gathering devices with blockchain’s ability to create a secure, immutable, and shared ledger. This integration creates a single, verifiable source of truth for physical events, solving critical challenges for organizations in Web3, AI, and carbon sectors.
This guide is for product teams, founders, and enterprise leaders who need to build unwavering trust and automate key processes using verifiable device data. We will explore how BIoT works, its real-world applications, and the implementation roadmap to help you build, scale, and execute effectively.
What is the Blockchain Internet of Things (BIoT)?
The Blockchain Internet of Things (BIoT) is an architecture designed to solve the core trust and security problems of traditional IoT systems. Standard IoT networks rely on centralized servers to manage data from devices, creating a single point of failure that is vulnerable to manipulation, hacks, or system glitches.
Blockchain addresses this by introducing a decentralized, tamper-proof layer. Imagine your IoT sensors as trusted agents reporting from the field. The blockchain then acts as a global, incorruptible notary that verifies and permanently records every report. Once a sensor’s data is written to the chain, it cannot be altered or deleted, ensuring complete data integrity from the moment of creation.
This synergy moves organizations from systems of uncertain data to networks built on verifiable truth. You can explore our detailed guide for more on how blockchain and IoT are building a secure, transparent future.
How Blockchain Solves Core IoT Challenges
The integration of blockchain technology directly addresses the fundamental weaknesses of legacy IoT deployments. The table below outlines how this convergence creates measurable enterprise value by solving for security, transparency, and automation.
| IoT Challenge | Blockchain Solution | Enterprise Impact |
|---|---|---|
| Centralized Security Risks | Data is distributed across a decentralized network, eliminating single points of failure. Cryptographic links secure every record. | Drastically improves resilience against hacks and data breaches, protecting mission-critical infrastructure. |
| Data Tampering & Fraud | The immutable ledger ensures that once IoT data is recorded, it cannot be altered or deleted. | Creates a verifiable, tamper-proof audit trail for compliance, supply chain tracking, and asset verification. |
| Lack of Transparency | A shared, distributed ledger provides all authorized parties with the same view of the data, creating a single source of truth. | Fosters trust between business partners, regulators, and customers, reducing disputes and operational friction. |
| Manual & Slow Processes | Smart contracts automatically execute actions—like payments or reporting—when triggered by verified IoT data. | Enables secure automation of complex business logic, accelerating settlements and reducing administrative overhead. |
Key Benefits of BIoT for Enterprises
This combination of IoT and blockchain delivers several powerful advantages that standalone systems simply can’t match:
- Enhanced Security: By distributing data across a decentralized network, BIoT gets rid of single points of failure. Cryptographic hashing makes sure every piece of data is securely linked to the last, creating a chain that is incredibly resilient and tamper-resistant.
- Guaranteed Data Integrity: Blockchain’s immutability means that once IoT data hits the ledger, it’s permanent. This is non-negotiable for any application that needs a flawless audit trail, like supply chain management or carbon credit reporting.
- Increased Transparency and Trust: Every authorized participant on the network sees the exact same ledger. This shared visibility builds trust between different parties because everyone is working from a single, undisputed set of facts.
- Improved Automation: Smart contracts are a game-changer here. They are essentially self-executing agreements where the terms are written directly into the code. When verified data from an IoT device comes in, a smart contract can be triggered to automate complex business processes—like releasing a payment upon confirmed delivery or issuing a carbon credit once a sensor verifies new forest growth.
How Do BIoT Systems Work?
The true potential of the Blockchain Internet of Things (BIoT) is not just in data collection; it’s in transforming a simple sensor reading into a verifiable, automated, and high-value event on a digital ledger. This process builds an architecture where physical actions create undeniable digital consequences.
It all starts at the network’s edge. Edge devices—the IoT sensors and gateways out in the field—are the first point of contact. They could be monitoring a shipment’s temperature, tracking a package’s location, or measuring energy consumption.
To guarantee data integrity from the very beginning, these devices cryptographically sign every piece of data they collect. Think of this digital signature as a tamper-proof seal, proving the data originated from a specific, trusted device and hasn’t been modified since.
This signed data then moves to an IoT gateway, which bundles information before sending it toward the blockchain. This is where architects face a crucial decision that directly impacts the system’s performance, cost, and scalability.
On-Chain Versus Off-Chain Data Strategies
A fundamental architectural choice in BIoT design is deciding what data to store on-chain versus off-chain. This decision represents a critical trade-off between absolute security, speed, and operational cost, and getting it right is essential for building a scalable system.
On-Chain Data: This involves writing data directly to the blockchain’s distributed ledger. It delivers the highest level of security and immutability but is also slower and more expensive. This approach is best reserved for the most critical information, such as transaction finality, ownership changes, or major compliance milestones.
Off-Chain Data: This is a more practical strategy for high-volume IoT data. Raw sensor readings are stored in a conventional database or a decentralized system like IPFS. Only a cryptographic hash—a unique digital fingerprint of that data—is recorded on-chain. This model is far more scalable and cost-effective, providing a tamper-evident link to the full dataset without overwhelming the blockchain.
For nearly all enterprise-scale BIoT applications, an off-chain strategy is the default choice. It strikes the necessary balance between verifiable proof and the practical reality of managing millions of data points, keeping the system efficient and affordable.
This flow diagram illustrates how data travels from a physical sensor to its final, verified state in a typical BIoT architecture.
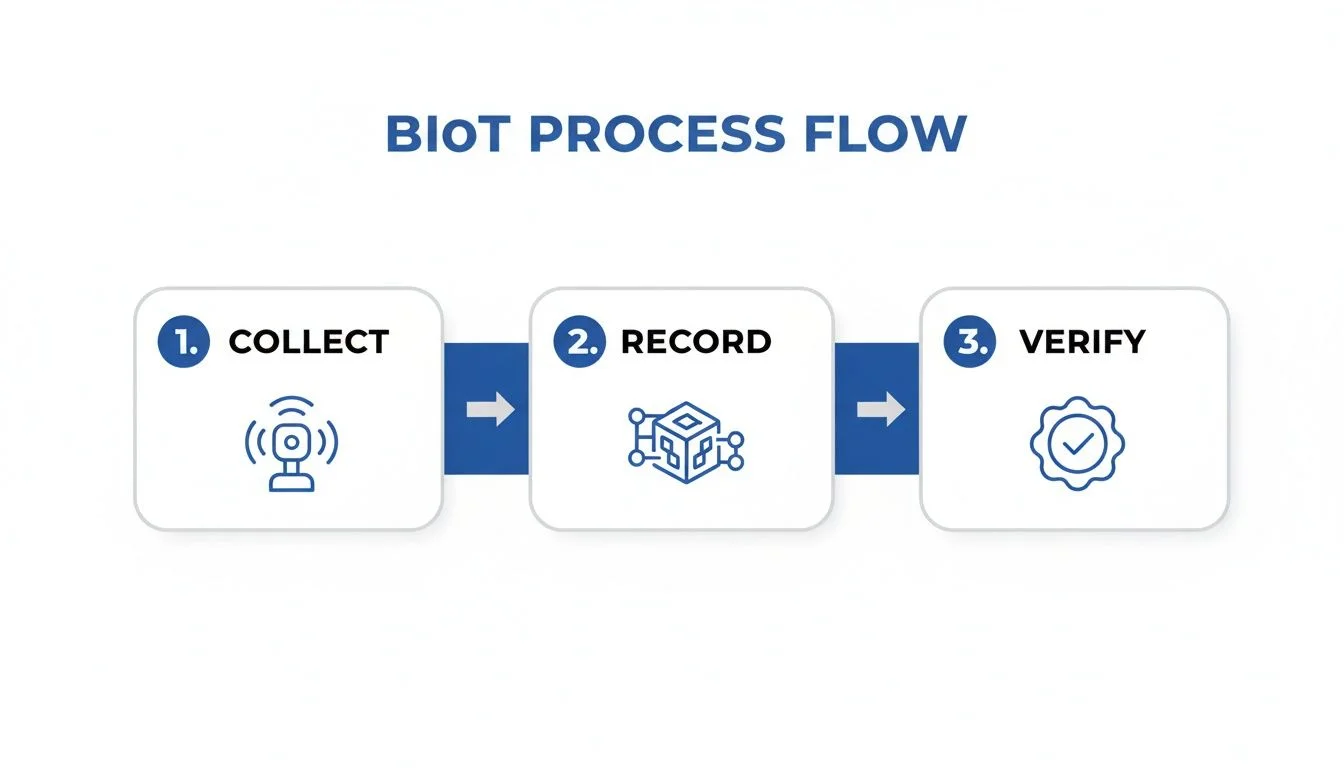
This journey from physical capture to immutable record forms the entire basis of trust in a BIoT ecosystem.
How do Oracles Connect IoT to Blockchain?
A blockchain cannot natively interact with real-world data. It needs a secure bridge, which is the job of an oracle—a trusted service that finds, verifies, and feeds external data to smart contracts.
In a BIoT system, oracles are essential. They connect off-chain IoT data streams to on-chain business logic, enabling powerful automation. For instance, an oracle can feed verified GPS data from a logistics sensor to a smart contract, which then automatically triggers a payment once the delivery is confirmed. This eliminates manual checks and builds a trustless, automated process.
For high-volume enterprise networks, Proof of Authority (PoA) has emerged as a preferred consensus mechanism. Instead of the energy-intensive Proof of Work, PoA relies on a set of pre-approved, trusted validators, making it significantly faster and more efficient. To handle even greater transaction loads, Layer-2 solutions like Polygon are often added to process transactions quickly and cheaply before bundling them into a single record on the main chain.
This multi-layered architecture is proving its worth in demanding sectors like India’s energy industry, which is adopting BIoT for smart grid management to meet its 2070 net-zero goals. One project connected 1 million smart meters to the Polygon blockchain, cutting energy theft by 29% and generating massive annual savings. You can find more examples in this survey of blockchain and IoT applications.
Advanced Security and Privacy in BIoT
While traditional IoT introduced unprecedented connectivity, it also created a vast new attack surface for cyber threats. The Blockchain Internet of Things (BIoT) fundamentally changes this by embedding security at its core rather than treating it as an afterthought. This re-engineering delivers sophisticated, provable security and privacy guarantees.
The strength of BIoT’s design comes from its deep roots in cryptographic principles. To really grasp the benefits, it helps to understand how cryptography protects network security systems, because every single device interaction is anchored by these mathematical proofs. It’s how we know for a fact that each piece of data is authentic and hasn’t been meddled with.

This cryptographic foundation enables one of BIoT’s most powerful features: tamper-resistant device identity management. In a typical centralized IoT setup, a single compromised server can become a gateway for rogue devices. BIoT is different. Each device gets a unique cryptographic identity on the blockchain—a digital passport that simply cannot be forged.
Fortifying The Network Edge
With this decentralized identity model, there’s no single point of failure that can be tricked into onboarding a fraudulent device. Before any new device can transmit data, it must be cryptographically verified by the network. This one change slams the door on a whole host of common infiltration tactics. For any enterprise managing a fleet of remote sensors, it’s a game-changing security upgrade.
Beyond just locking things down, BIoT also unlocks advanced privacy models that are just not feasible in traditional systems. Think about it: companies often need to prove a condition was met without giving away the sensitive data behind it. A pharmaceutical company, for example, needs to verify a shipment stayed within a temperature range, but they certainly don’t want their precise thermal data—a piece of proprietary information—made public.
This is where Zero-Knowledge Proofs (ZKPs) come in.
Zero-Knowledge Proofs allow a party to prove that a statement is true (e.g., ‘this device reading is within compliant parameters’) without revealing any of the specific data behind that statement. It’s the digital equivalent of proving you have a key to a room without showing the key itself.
Using ZKPs, an IoT device can submit a cryptographic proof to the blockchain confirming its data meets a certain standard. A smart contract can then verify this proof and trigger an action, all without the raw, sensitive data ever hitting a public ledger. If you want to go deeper on this, check out our piece on how Zero-Knowledge Proofs are advancing blockchain privacy and security.
Creating An Immutable Audit Trail For Compliance
In regulated industries, being able to produce a perfect, unchangeable audit trail isn’t just a nice-to-have—it’s a strict requirement. This is especially true for sectors like Real World Asset (RWA) tokenisation and carbon credit markets, where absolute trust in the data is everything.
BIoT delivers this automatically. Every verified event from an IoT sensor—whether it’s the confirmed location of a tokenised asset or the measured carbon sequestration from a forestry project—gets logged on an immutable ledger. This creates a golden record that regulators, auditors, and investors can trust without a second thought.
This complete, time-stamped history offers a few key advantages:
- Regulatory Adherence: It makes reporting for standards like ESG (Environmental, Social, and Governance) far simpler by providing verifiable, device-generated data.
- Dispute Resolution: In commercial deals, a blockchain-based record of events can instantly settle arguments over performance or delivery.
- Asset Verification: For RWA tokenisation, it gives you undeniable proof of an asset’s condition and location, which directly underpins its value.
By weaving together decentralized identity, advanced privacy techniques, and immutable ledgers, BIoT builds a security posture that is orders of magnitude stronger than legacy IoT architectures.
Real-World BIoT Applications Driving Growth
While the technical architecture is impressive, the true test of Blockchain IoT (BIoT) lies in the tangible business value it creates. Across industries, organizations are leveraging BIoT to solve long-standing problems related to trust, transparency, and automation. These applications demonstrate how linking physical assets to an immutable ledger unlocks new efficiencies and revenue streams.
The core power of BIoT is its ability to forge a verifiable, unbreakable connection between the physical world and a digital record. This turns sensor data from a simple observation into an undeniable fact, creating immense value where proof is everything.

Securing High-Value Supply Chains
Global supply chains for high-value goods like pharmaceuticals, precious metals, and luxury items are plagued by counterfeiting and theft. Legacy tracking systems are often siloed and rely on centralized databases that can be hacked or altered. BIoT provides a direct solution by creating a bulletproof, real-time chain of custody.
Let’s track a gold bar from the mine to a secure vault.
- The Problem: At every touchpoint—mining, refining, transport, and storage—there are risks. A genuine bar could be swapped for a lower-purity fake, or its paper trail could be forged.
- The BIoT Solution: An IoT device with GPS and tamper-evident seals is attached to the asset. This device logs its location, movement, and integrity status, signing each data point and anchoring it to a blockchain. This creates a permanent, verifiable history.
- The Outcome: Any party in the supply chain can instantly confirm the asset’s provenance. This doesn’t just reduce fraud; it dramatically lowers insurance premiums and boosts the asset’s market value by guaranteeing its authenticity.
This model is already delivering results. In India, a 2023 pilot project monitoring over 500,000 IoT-enabled pharmaceutical shipments led to a 35% reduction in counterfeit drugs and a 28% drop in logistics costs. You can explore the data behind these supply chain advancements on ijcsm.researchcommons.org.
Building Investor Trust in Real World Assets
The tokenization of Real World Assets (RWAs) is one of the fastest-growing sectors in decentralized finance. For an RWA token to hold value, investors need absolute confidence that the underlying physical asset exists and is in the condition claimed. BIoT provides this critical layer of physical-world verification.
Imagine a portfolio of tokenized fine art held in a secure vault.
By linking a digital token to live, verified data from the physical world, BIoT solves the “garbage in, garbage out” problem. It ensures the on-chain representation of an asset accurately reflects its off-chain reality, building the foundational trust needed for the RWA market to scale.
IoT sensors inside the storage unit monitor temperature, humidity, and security around the clock. This data is fed through an oracle to the smart contract governing the RWA tokens. If conditions stray from the agreed-upon parameters, an alert is automatically triggered on-chain, notifying all token holders. This real-time, tamper-proof monitoring gives investors the continuous assurance they need, making the asset far more liquid and attractive. This same principle is foundational for creating digital twins of complex infrastructure. For more on this, read also: our guide on how blockchain and digital twins are revolutionizing smart cities.
Generating High-Integrity Carbon Credits
In the sustainability sector, the credibility of carbon credits is often undermined by poor monitoring and opaque verification processes. BIoT offers a solution by enabling the generation of high-integrity, data-backed carbon credits that are fully auditable and transparent.
Consider a reforestation project. IoT sensors deployed across a forest can measure soil moisture, track tree growth rates, and monitor atmospheric carbon levels. This raw data is aggregated, and its cryptographic hash is anchored to the blockchain. Based on this verified data, a smart contract can then automatically issue a corresponding number of carbon credits as digital tokens.
This process establishes a transparent and irrefutable link between the physical act of carbon sequestration and the digital credit, stamping out issues like double-counting and fraud. This high-integrity data can also fuel sophisticated decentralized prediction markets, where traders can speculate on future environmental outcomes based on trusted, real-time sensor feeds.
Your BIoT Implementation Roadmap and Tech Stack
Moving a great idea from a whiteboard to a real-world product demands a clear, structured plan. Building your first Blockchain Internet of Things (BIoT) solution can feel daunting, but breaking the journey down into a methodical roadmap—from a focused proof-of-concept to a full-scale deployment—makes all the difference. This approach helps you sidestep common pitfalls and get to market faster.
It all starts with one question: what specific business problem are you solving? Forget vague goals like “using BIoT.” Instead, get precise. A much better target is something like, “We will reduce counterfeit components in our spare parts supply chain by 20% using verifiable, device-level tracking.” A sharp, measurable objective like this will guide every technical choice you make from here on out.
Next, you have to think about the hardware. Your choice of IoT devices and gateways is absolutely critical, and it depends entirely on your use case and the environment they’ll be operating in.
Choosing Your Core Technology Components
With a clear problem and your hardware in mind, it’s time to select a blockchain platform. This is a balancing act between decentralization, security, cost, and performance. Public Layer-2 networks like Polygon offer impressive speed and lower fees, making them a great fit for projects that need public verifiability. On the other hand, private blockchains like Hyperledger Fabric give you maximum control over privacy and performance, which is often what enterprise consortiums are looking for.
Alongside the blockchain itself, you’ll need to design your smart contracts. Think of these as the automated rulebooks for your BIoT system. They must be coded meticulously to execute specific actions—like releasing a payment or updating an asset’s status—but only when triggered by verified IoT data delivered by an oracle. As you map out your BIoT implementation and tech stack, remember that reliable industrial connectivity solutions form the backbone that ensures your devices can consistently talk to the network.
Recommended Tech Stacks and Design Patterns
The right tech stack looks very different for an agile startup than it does for a security-obsessed enterprise. There’s no one-size-fits-all answer here. The best choice is one that lines up with your team’s resources, risk tolerance, and long-term scalability goals.
For an agile startup or pilot project:
- IoT Hardware: Flexible and inexpensive devices like Raspberry Pi or Arduino are perfect for getting a prototype up and running quickly.
- Connectivity Protocol: MQTT is a lightweight messaging protocol that’s become a standard for IoT because it works well with constrained devices and over unreliable networks.
- Blockchain Platform: A public L2 such as Polygon or Arbitrum gives you decentralization and security without the headache and cost of managing your own network infrastructure.
- Oracle Network: Using an established network like Chainlink is the simplest way to securely get real-world IoT data into your smart contracts.
This stack is all about speed-to-market and keeping initial costs low.
The key is to start with a focused proof-of-concept (PoC). A successful PoC validates your core assumptions and builds the business case for a larger investment, making it much easier to get the resources you need for a full-scale rollout.
For a security-focused enterprise deployment:
- IoT Hardware: Industrial-grade gateways and hardened sensors are non-negotiable. They’re built to withstand harsh environments and deliver rock-solid reliability.
- Connectivity Protocol: Protocols like OPC-UA are often preferred in industrial settings for their robust security features and sophisticated data modeling.
- Blockchain Platform: A private or consortium blockchain like Hyperledger Fabric provides the granular control over data privacy, access, and governance that is critical for most enterprise use cases.
- Oracle Network: A private or custom-built oracle network might be necessary to satisfy specific compliance and security mandates.
This enterprise stack puts security, control, and long-term scalability ahead of initial development speed. By carefully thinking through these roadmaps and tech stacks, you can build a BIoT solution that’s not only technically sound but also perfectly aligned with your business objectives.
How Blocsys Helps You Build with BIoT
Turning the concept of the Blockchain Internet of Things (BIoT) into a production-ready system demands specialised expertise. At Blocsys, we don’t just understand the theory; we have first-hand experience building and scaling the blockchain and AI platforms that make BIoT work for fintechs, exchanges, and digital asset businesses.
Our work is centred on solving complex BIoT challenges to create tangible business solutions. Whether you’re building a secure RWA tokenisation platform that depends on verified sensor data or developing a high-integrity carbon credit system, our team has the practical knowledge to architect and deploy it. This is more than just writing code—it’s about designing secure, scalable, and enterprise-grade infrastructure.
From Vision to Reality
We specialise in transforming ambitious BIoT concepts into operational realities. Our expertise covers the full spectrum of development, from designing tokenisation systems and trading infrastructure to building intelligent compliance workflows. We know the specific hurdles Web3 companies face and provide the targeted support needed to overcome them.
For Blocsys, BIoT is not a future concept—it is a present-day reality we deliver. We have a proven track record of enabling organisations to build, scale, and execute effectively in the Web3 space.
This deep experience is clear in real-world deployments. India’s smart agriculture sector, for instance, has seen explosive growth through BIoT. A recent government initiative deployed IoT soil sensors across 50,000 hectares, linked to a Hyperledger Fabric blockchain, which led to a 22% increase in crop yields. Blocsys has powered similar platforms for agri-fintechs, integrating AI for predictive analytics on these crucial IoT feeds. You can learn more about the global growth in connected devices at IoT Analytics.
We act as your dedicated partner, helping you navigate the complexities of BIoT to build platforms that deliver real value. Our goal is to empower you to achieve your specific business objectives with robust and reliable technology.
Ready to build the next generation of trusted, automated systems? Connect with our experts today to discuss how Blocsys can help you achieve your goals with a secure, scalable BIoT solution.
Frequently Asked Questions About BIoT
When we talk to clients about combining blockchain with the Internet of Things, a few key questions always come up. Whether you’re a decision-maker weighing the strategic fit or a technical leader planning the implementation, these are the practical answers you need.
What Is the Biggest Challenge in Combining Blockchain and IoT?
The single biggest hurdle in combining blockchain and IoT is scalability. IoT networks can generate a massive volume of data every second, while most blockchains have limited transaction throughput. This creates a natural bottleneck that can hinder performance and drive up costs.
The solution is a hybrid, multi-layered architecture. Best practices involve:
- Off-Chain Storage: Keeping high-volume, raw sensor data in an efficient off-chain system.
- On-Chain Anchoring: Recording only critical data points or cryptographic hashes on the blockchain for verification.
- Layer-2 Solutions: Using scaling networks to process transactions quickly and affordably.
This balanced approach provides security and verifiability without sacrificing performance.
Can I Use a Public Blockchain for an Enterprise IoT Project?
Yes, you can use a public blockchain for enterprise IoT, but it requires a strategic approach. While public Layer-1 blockchains like Ethereum offer unparalleled security and decentralization, their high transaction fees (gas costs) and slower speeds can be impractical for high-volume IoT data.
A more effective strategy for enterprises is to use public Layer-2 networks such as Polygon or Arbitrum. These platforms provide much lower fees and faster transaction finality while still inheriting the security of the underlying mainnet. For use cases demanding maximum privacy and control, a private or consortium blockchain like Hyperledger Fabric remains a strong alternative.
How Much Does a Blockchain IoT Solution Cost to Implement?
The cost of a BIoT solution varies widely based on scope and complexity. A small-scale proof-of-concept (PoC) to validate a single use case might start in the tens of thousands of dollars, whereas a full, enterprise-wide deployment can run into the millions.
Your main cost drivers will be:
- IoT Hardware: The number and sophistication of your sensors, gateways, and other edge devices.
- Blockchain Platform: Transaction fees on a public chain versus the infrastructure and upkeep of a private one.
- Development: The complexity of your smart contracts, oracle integrations, and any custom applications for users.
- Integration: The work needed to connect your BIoT system to existing enterprise software like an ERP or supply chain platform.
Our advice is always to start small with a tightly-focused pilot project. This lets you prove the technology works and demonstrate a clear return on investment (ROI) before you commit to a larger, more complex rollout.
Is BIoT Completely Secure from Hacking?
BIoT offers a significant security upgrade over traditional IoT, but no system is invulnerable. The blockchain ledger itself is exceptionally resistant to tampering, creating an immutable audit trail.
However, vulnerabilities can still exist at other layers of the system. The most common weak points are the physical IoT devices themselves (e.g., firmware exploits) or bugs within the smart contract code. A comprehensive security strategy must be end-to-end, involving hardware hardening, rigorous smart contract audits, and end-to-end data encryption from sensor to ledger.