A blockchain record system handling 3,500 schools, 5 million students, and 750,000 teachers in Ethiopia shows what most executives still underestimate about document verification. At enterprise scale, the core challenge isn’t whether blockchain can prove a record existed. It’s whether organisations can build a verification fabric that remains trustworthy across regulators, counterparties, and fragmented systems while preserving privacy and auditability. That benchmark comes from a peer-reviewed analysis of the Ethiopian credential initiative, which also notes that analogous pilots reduced verification times by up to 90% through blockchain-based authentication workflows (peer-reviewed analysis).
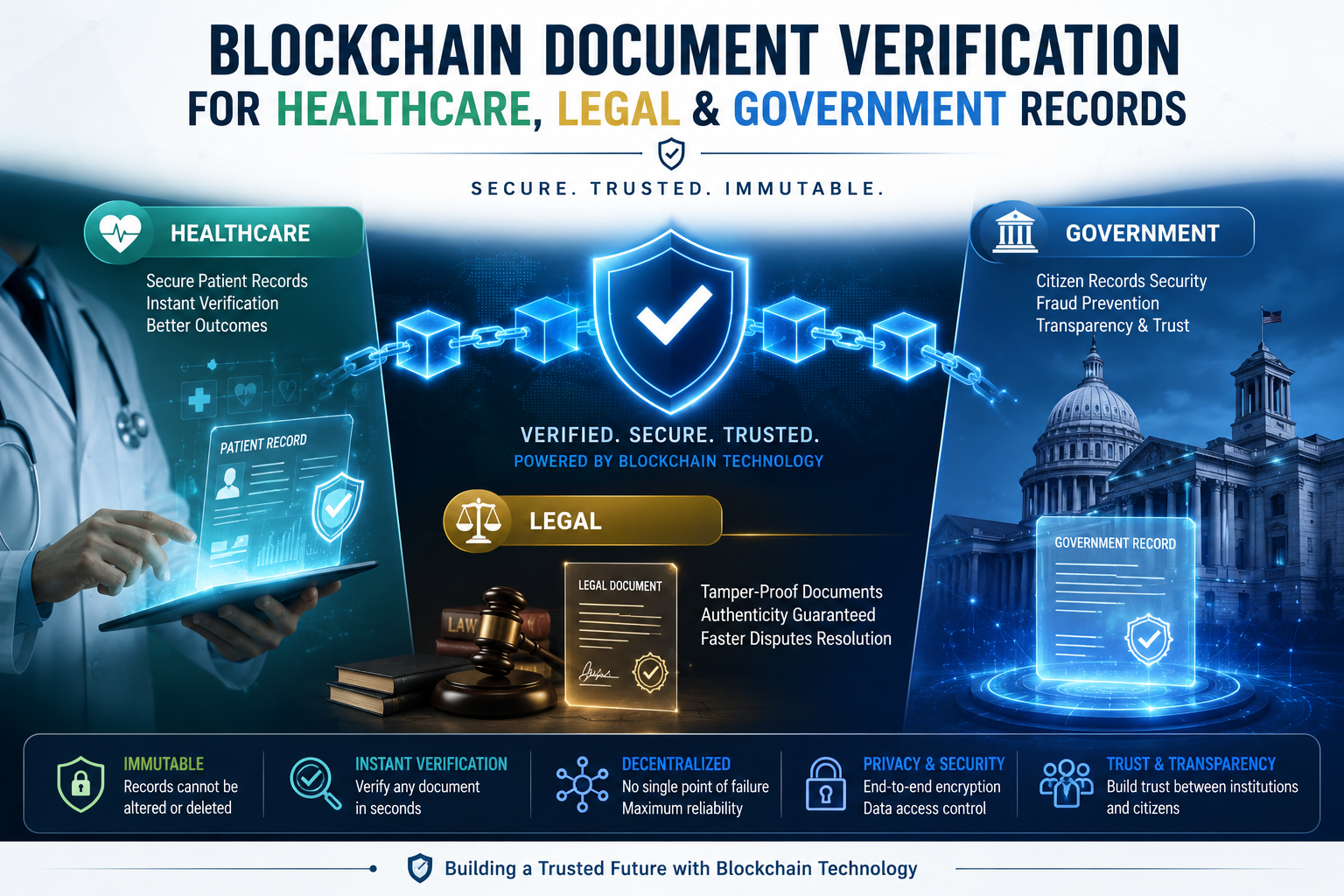
For healthcare providers, legal operators, government agencies, and enterprise software teams, that shifts the conversation. Blockchain document verification is no longer a speculative concept. It’s an architectural option for tamper-proof document verification, decentralised identity verification systems, and immutable blockchain records that can reduce manual checking, strengthen audit trails, and make fraud materially harder.
This guide is written for decision-makers evaluating production deployment. It explains where centralised systems fail, how blockchain verification works in practice, where it fits across regulated sectors, and why the overlooked issue is no longer immutability alone. It’s interoperability.
Table of Contents
- The Trust Deficit in Centralised Record Keeping
- How Blockchain Creates Tamper-Proof Document Verification
- Centralised vs Blockchain Verification A Strategic Comparison
- Use Cases Across Healthcare Legal and Government Sectors
- Integrating AI for Advanced Fraud Prevention and Automation
- The Next Frontier Overcoming Interoperability Challenges
- How Blocsys Engineers Enterprise-Grade Verification Infrastructure
- Frequently Asked Questions about Blockchain Verification
- What is blockchain document verification
- How does blockchain secure healthcare records
- Why should government agencies use blockchain verification systems
- What is tamper-proof document verification
- How does blockchain prevent document fraud
- What are immutable blockchain records
- How do decentralised identity verification systems work
- What is the difference between centralised and blockchain verification systems
- How secure is blockchain authentication for legal documents
- What industries benefit from blockchain document verification
The Trust Deficit in Centralised Record Keeping
Centralised record systems create efficiency inside a single organisation, but trust breaks down the moment verification crosses institutional boundaries. A hospital may trust its own database. A court may trust its case management platform. A ministry may trust its internal registry. None of those systems automatically gives a third party confidence that a document hasn’t been altered, backdated, duplicated, or exported without context.
That’s the core trust deficit. It isn’t just about cyber risk. It’s about verifiable integrity across organisations.
Why legacy audit trails break under pressure
Traditional systems rely on administrator privileges, internal logs, and perimeter security. Those controls matter, but they also create a familiar failure pattern:
- Single administrative authority: privileged users can modify records, permissions, or retention settings.
- Fragmented audit history: logs are often stored separately from the documents they describe.
- Version ambiguity: teams may circulate PDFs, scans, and exports with no shared source of truth.
- Manual cross-checking: verification moves through email chains, portals, or phone calls rather than cryptographic proof.
In healthcare, that can slow provider onboarding, data-sharing approvals, and record validation. In legal environments, it can complicate chain-of-custody confidence and timestamp reliability. In government, it often leads to paperwork loops where citizens and counterparties resubmit records that another public body already holds.
Practical rule: If a verifier must call the issuer to confirm authenticity, the verification architecture hasn’t solved trust at scale.
The business case is broader than fraud prevention
Executives often frame blockchain verification as an anti-fraud tool. That understates the value. The stronger business case is operational.
When records are difficult to verify, organisations pay in slower workflows, duplicated reviews, inconsistent decisions, and avoidable compliance friction. The cost appears in onboarding delays, procurement bottlenecks, disputes over document lineage, and weak interoperability between regulated entities.
A secure document system in regulated sectors needs four properties at once:
| Requirement | Why it matters |
|---|---|
| Integrity | The record must show whether any unauthorised change occurred |
| Provenance | Verifiers need to know who issued it and under what authority |
| Auditability | Compliance teams need a reconstructible history |
| Portability | The record must be verifiable outside the issuer’s own system |
Centralised architecture usually handles one or two of these well inside a controlled boundary. It struggles when all four are required across organisations, jurisdictions, and technology stacks.
That’s why blockchain document verification matters. It changes verification from a trust-me process into a prove-it process.
How Blockchain Creates Tamper-Proof Document Verification
In document-intensive sectors, tamper evidence is only one part of the design problem. The harder requirement is proving integrity, issuer authority, and current validity across organisations that do not share the same database, legal framework, or blockchain network.

What the blockchain verification flow looks like
A production system usually follows a five-step pattern:
-
A source document is issued or finalised.
Examples include a physician credential, court filing, licence, permit, contract, or compliance certificate. -
The system generates a cryptographic hash.
This creates a unique fingerprint of the file. A one-character edit produces a different hash. -
The hash is anchored to a blockchain ledger.
The ledger records the timestamp, issuing entity, and, in some designs, workflow approvals or policy references. -
A verifier checks the document later.
The verifier hashes the presented file and compares that output with the anchored value. -
Any mismatch is visible immediately.
Integrity verification becomes deterministic. The verifier does not need to rely on screenshots, email trails, or manual confirmation from the issuer.
This model is stronger than simple file comparison because it adds independent proof. The document itself usually stays off-chain in an existing repository or document management system. What goes on-chain is the evidence layer: hash, timestamp, issuer reference, credential status, and other verification metadata.
That architecture matters in regulated environments. Healthcare, legal, and public-sector records often contain sensitive data that should not be written to a public ledger. Hash anchoring preserves privacy while still giving external parties a way to verify that the record has not been altered since issuance.
DIDs and VCs extend integrity into trustable issuer identity
Hashing proves a file is unchanged. It does not prove that the file came from an authorised issuer, or that the credential is still valid at the moment of review.
Enterprise-grade verification systems address that gap with Decentralised Identifiers (DIDs) and Verifiable Credentials (VCs). DIDs bind a credential to a cryptographic identity controlled by the issuer. VCs package the claim in a standard format that other systems can validate without direct access to the issuer’s internal database. Revocation registries and status checks then show whether the credential remains in force.
That combination is particularly important in cross-jurisdiction workflows. A hospital, bar association, court, insurer, and government agency may each use different systems and trust frameworks. In practice, the verification layer has to work across those boundaries. A single-chain proof of concept is rarely enough if counterparties operate on different ledger networks or require standards-based verification that survives platform changes.
As noted earlier, the Acorn Healthcare Credentialing case study illustrates how issuer identity, credential status, and automated verification can reduce manual review time while improving fraud detection, using a DID- and VC-based model with privacy-preserving controls.
A useful way to evaluate the stack:
- Hashing proves the file has not changed
- DIDs identify the issuer cryptographically
- VCs package claims in a portable, machine-verifiable format
- Revocation registries show whether the credential is still valid
- Smart contracts or policy engines apply verification rules consistently across parties
- Interoperability layers translate proofs across chains, standards, and jurisdictional requirements
For teams assessing architecture options, this explanation of digital proof of document integrity provides a useful reference model.
Blockchain verification shifts trust from private system control to cryptographic proof, issuer governance, and interoperable validation standards.
Centralised vs Blockchain Verification A Strategic Comparison
The strategic question isn’t whether blockchain replaces every database. It won’t. The sharper question is where organisations need a database for storage and where they need a ledger for independent proof.

What executives should compare first
A centralised repository is usually effective when one organisation owns the process, controls access, and accepts internal trust assumptions. Blockchain verification becomes more attractive when multiple independent parties need to validate the same records without relying on a single operator.
The architectural trade-off looks like this:
- Centralised systems optimise for control
- Blockchain systems optimise for shared verifiability
That distinction matters more than technical ideology. Most mature enterprise deployments end up hybrid. Core documents may stay in existing repositories, while verification proofs, credential status, and workflow attestations are anchored to a blockchain layer.
Feature Comparison Centralised vs Blockchain Verification Systems
| Feature | Centralised Systems (e.g., SQL Database) | Blockchain Verification Systems |
|---|---|---|
| Security model | Perimeter and admin-control based | Distributed trust with cryptographic anchoring |
| Failure mode | Single operational authority can become a single point of failure | Resilience improves because history is shared and harder to rewrite |
| Document integrity | Records can be altered if permissions allow | Immutable ledger design makes tampering evident |
| Audit trail | Logs may be partial, siloed, or editable | Timestamped history is append-only and easier to verify |
| Cross-party verification | Often requires portal access or issuer confirmation | Independent verifiers can check proofs directly |
| Privacy handling | Mature access controls, but trust stays centralised | Strong when paired with off-chain storage and selective disclosure |
| Regulatory posture | Familiar for legacy teams | Strong for traceability when designed around sector rules |
| Change management | Easier for internal-only deployments | Better suited for multi-party trust frameworks |
One useful benchmark for teams comparing architectural models is this review of blockchain vs traditional systems, especially when the goal is external verification rather than internal record-keeping alone.
A blockchain ledger is rarely the whole application. It’s the verification layer that makes a broader application harder to manipulate and easier to audit.
Where blockchain is the better fit
Blockchain verification tends to be the stronger option when organisations need:
- Independent proof across entities
- High-confidence auditability
- Tamper evidence without manual reconciliation
- Portable credentials for regulators, partners, or citizens
A centralised model usually remains suitable for internal drafts, transient workflow data, and records that never leave one trust boundary.
Use Cases Across Healthcare Legal and Government Sectors
Analysts and regulators keep reaching the same conclusion: document fraud, broken audit trails, and slow inter-organisational verification impose costs far beyond IT. The sectors with the clearest return on blockchain verification are the ones where a single disputed record can delay care, trigger litigation, suspend a licence, or undermine public confidence. In practice, the harder problem is not anchoring one file on one chain. It is proving authenticity across organisations, jurisdictions, and technical stacks that were never designed to trust one another.

Healthcare
Healthcare verification fails less often at the point of record creation than at the point of exchange. Hospitals, insurers, regulators, labs, research sponsors, and cross-border care networks often rely on different systems of record, different identity models, and different retention rules. A blockchain verification layer helps establish a shared proof model without forcing every participant onto one application stack.
For regulated electronic records, 21 CFR Part 11 requires controls that support auditability, traceability, and record reconstruction. Blockchain supports those controls when it is implemented as a verification layer tied to signed events, document hashes, and policy-based off-chain storage. A clinical research study in Frontiers in Blockchain found that blockchain-based audit trails could generate human-readable exports aligned with FDA expectations and materially reduce integrity risk in simulated submission workflows (Frontiers in Blockchain analysis).
The strategic use cases are clear:
- Provider credentialing across institutions. Verifiers need to confirm licences, certifications, sanctions status, and employment history without waiting for manual callbacks from every issuer.
- Clinical trial documentation. Sponsors, CROs, and regulators need a defensible chronology for protocol amendments, consent records, and submission artefacts.
- Patient-directed record sharing. Patients need to present verifiable records across networks and sometimes across borders, while the underlying clinical data remains off-chain.
- Claims and reimbursement disputes. Payers and providers need proof that supporting documents are authentic, time-bound, and unchanged since submission.
Interoperability determines whether these deployments scale. A hospital may anchor proofs on one network, while a regulator, insurer, or partner clinic verifies through another trust framework entirely. That is why blockchain in healthcare and securing data interoperability matters more than isolated pilots built around a single ledger.
For finance and compliance leaders, document verification also intersects with retention and accounting controls. SamSearch on FAR accounting principles is a useful reference for understanding how record-keeping obligations shape downstream verification design.
Legal
Legal teams care about chronology, custody, and admissibility. Those requirements often span law firms, clients, courts, outside experts, e-discovery vendors, and counterparties that do not share infrastructure or trust assumptions. That makes legal verification a cross-party coordination problem as much as a records problem.
Three use cases consistently justify investment.
-
Evidence logging and chain of custody
Teams can anchor document fingerprints at collection, review, transfer, and production. That reduces room for procedural disputes over whether evidence was altered between handoffs. -
Contract authenticity and version control
Signed agreements can be hashed and timestamped so disputes focus on obligations, not on whether the signed version is the same version presented later. -
Intellectual property timestamping
Enterprises can register proof of existence for drafts, invention disclosures, and supporting files before filing, licensing, or disclosure events.
The overlooked issue is jurisdictional portability. A proof anchored in one legal or technical environment still has to be explained, verified, and sometimes translated for another. Enterprises that expect blockchain to support litigation, cross-border transactions, or multi-firm workflows should design for standards-based verification outputs and independent validation paths from the start.
A short explainer is useful before the next example:
Government
Government verification systems face the widest trust boundary. Citizens, agencies, auditors, courts, service providers, and foreign counterparties may all need to validate the same credential or record, often without direct access to the issuing system. That makes interoperability a first-order architecture decision, not a later optimisation.
The strongest public-sector use cases include:
- Licences and permits
- Land and property records
- Civil certificates
- Professional accreditations
- Cross-agency digital identity assertions
Each category looks different operationally, but the architectural pattern is similar. The issuing authority keeps its system of record. The verification layer publishes tamper-evident proofs, status changes, and issuer metadata in a format external parties can check independently. That model becomes even more important when one ministry uses one ledger, another uses a different stack, and external verifiers sit in another jurisdiction altogether.
Cross-chain and cross-jurisdiction design is where many public pilots stall. A national education registry, health credential network, or civil records system may work inside one programme boundary and still fail to support banks, employers, foreign agencies, or regional authorities that need to verify credentials through different technical rails. A well-designed tamper-proof document verification platform addresses that gap by preserving existing systems of record while adding a verification layer that can be checked outside the issuer’s own portal.
Integrating AI for Advanced Fraud Prevention and Automation
Blockchain proves whether a verified record changed after issuance. AI helps determine whether the record should be trusted before it is ever anchored. Together, they create a stronger control model than either technology delivers alone.

Where AI fits before and after blockchain anchoring
AI is most useful in two moments.
First, before registration, models can inspect files for anomalies such as inconsistent formatting, suspicious image edits, unusual metadata patterns, or mismatched fields across structured and unstructured inputs. That supports intake teams dealing with scanned forms, certificates, identity artefacts, and legacy PDFs.
Second, after anchoring, AI can monitor verification activity itself. It can flag unusual access patterns, repeated submission attempts, inconsistent credential chains, or suspicious revocation behaviour.
That creates a feedback loop:
- AI screens for probable fraud signals
- Blockchain anchors only approved proofs
- The anchored history becomes a cleaner compliance dataset
- Future AI models learn from a more trustworthy event trail
What automation changes operationally
Smart contracts add the third layer. Once AI and blockchain produce a high-confidence state, smart contracts can automate business decisions.
Examples include:
- Provider onboarding: activate only if credentials validate and revocation checks pass
- Document release: permit access only after approvals are recorded
- Claims progression: advance workflow when required records are present and unchanged
- Public service fulfilment: issue a digital approval when supporting evidence clears validation rules
For teams exploring this convergence in production systems, AI for blockchain is the relevant implementation lens. It shows why fraud prevention increasingly depends on connecting model-driven anomaly detection with immutable event recording rather than treating them as separate programmes.
One vendor in this space is Blocsys Technologies, which builds blockchain and AI infrastructure for production workflows where document integrity, automation, and compliance need to operate together rather than as disconnected tools.
The Next Frontier Overcoming Interoperability Challenges
Most blockchain verification articles stop at immutability. That’s no longer enough for enterprise planning.
A hospital group may use one chain or ledger framework. A national identity programme may use another. A legal counterparty may rely on a permissioned network with different credential standards. If those systems can’t verify one another’s assertions, the organisation hasn’t built a digital trust layer. It has built another silo.
Why single-chain thinking fails in enterprise environments
A healthcare interoperability review identifies this as a major gap. Existing literature covers immutability and audit trails well, but gives minimal attention to how blockchain verification systems can interoperate across different healthcare networks, legal jurisdictions, and government databases at the same time (HIPAA Vault discussion of blockchain integration gaps).
That gap has direct business consequences:
- Verification breaks at jurisdiction boundaries
- Credential portability becomes chain-specific
- Compliance workflows need custom bridges
- Procurement risk rises because architecture choices lock in future integration cost
For readers focused on the broader data side of this challenge, OMOPHub’s guide to data interoperability is useful context because it frames interoperability as an operational design issue, not just a standards checkbox.
What a cross-jurisdiction architecture needs
Enterprise teams should treat interoperability as a first-order design requirement. In practice, that means building around common credential semantics and verification services rather than assuming one ledger will dominate every participant.
A strong architecture usually needs:
| Design layer | What to standardise |
|---|---|
| Credential model | Shared VC schemas, issuer rules, revocation logic |
| Identity layer | DID methods and resolution policies |
| Proof layer | Hashing, timestamps, selective disclosure, audit evidence |
| Integration layer | APIs, middleware, and event connectors to legacy systems |
| Governance layer | Cross-organisation rules for trust, updates, and dispute handling |
Cross-chain strategy matters here. Teams planning for heterogeneous networks should understand blockchain interoperability for cross-chain dApps, because verification at scale depends less on choosing one perfect chain and more on designing a trust fabric that survives multiple chains.
The next competitive advantage won’t come from proving one record on one chain. It will come from making verified records portable across institutions that don’t share infrastructure or governance.
How Blocsys Engineers Enterprise-Grade Verification Infrastructure
Enterprise verification systems fail when teams treat them as a feature instead of a platform. Real deployments need policy design, identity architecture, integration planning, smart contract controls, storage strategy, and operational governance.
What enterprise delivery actually requires
Blocsys approaches this problem as infrastructure engineering. For organisations building regulated verification workflows, that usually means combining:
- Blockchain anchoring for integrity proofs
- Off-chain storage for sensitive records
- Credential frameworks for issuer trust
- Smart contract logic for approvals and revocations
- AI-assisted intake and fraud review
- Integration with existing enterprise software
For leadership teams assessing implementation routes, the practical entry points are the Blocsys home page and its work as a blockchain development company. Those pages are relevant because they align with the actual delivery model enterprises need: architecture, engineering, integration, and secure production rollout.
Talent planning also matters. Organisations that need to build in-house capability alongside a delivery partner can use this guide to find blockchain engineering talent to clarify the skill profiles typically required for these systems.
The strategic lesson is simple. Verification architecture touches compliance, cybersecurity, data governance, and product operations at once. That’s why the right partner isn’t just writing smart contracts. It’s engineering a system that auditors, regulators, counterparties, and internal teams can all rely on.
Frequently Asked Questions about Blockchain Verification
What is blockchain document verification
Blockchain document verification records a cryptographic hash of a document on a ledger so another party can later test whether the file is authentic and unchanged. The document itself usually remains outside the chain in a controlled repository, which matters in healthcare, legal, and government settings where privacy, retention, and access controls cannot be delegated to a public network.
How does blockchain secure healthcare records
It secures the verification process, not the clinical record by itself. A healthcare provider can anchor proof of issuance, updates, approvals, and revocations while keeping protected health information off-chain. That design improves auditability and chain of custody without creating unnecessary exposure of sensitive data.
Why should government agencies use blockchain verification systems
Government agencies often exchange records across departments, vendors, courts, and external jurisdictions that do not share a common database. Blockchain verification gives each party a common integrity layer for certificates, permits, land records, and identity documents. The business value increases when verification must work across institutional boundaries instead of inside a single agency stack.
What is tamper-proof document verification
It is the ability to detect whether a document changed after issuance or approval. In practice, the verifier recalculates the file hash and compares it with the earlier anchored proof. If the values differ, the document no longer matches the recorded version.
How does blockchain prevent document fraud
Blockchain reduces several common fraud paths. It exposes post-issuance edits, preserves a timestamped event history, and supports signed credentials tied to a known issuer. It does not stop every fraud scenario, especially those involving stolen keys or false data entered at the start, which is why production systems also need identity controls, approval workflows, and revocation handling.
What are immutable blockchain records
They are ledger entries that cannot be altered without detection after confirmation. For document verification, that immutability usually applies to hashes, signatures, timestamps, and status changes. Sensitive files, large attachments, and regulated data should usually stay off-chain for legal and operational reasons.
How do decentralised identity verification systems work
They use identifiers and verifiable credentials that can be checked cryptographically without calling the issuer every time. The issuer signs the credential, the holder presents it, and the verifier checks signature validity, issuer status, and revocation state. In cross-border or cross-chain deployments, that last step is often the hard part because trust registries, schema definitions, and revocation methods are rarely standardised across jurisdictions.
What is the difference between centralised and blockchain verification systems
A centralised system depends on one operator to store records and answer verification requests. A blockchain verification system adds a shared proof layer that independent parties can validate without relying on that operator alone. Large enterprises usually combine both models: central platforms manage content and policy, while blockchain supports external proof, audit evidence, and inter-organisational trust.
How secure is blockchain authentication for legal documents
Security depends less on the chain itself than on system design. Key custody, signer authority, smart contract controls, timestamp integrity, and evidentiary procedures determine whether a record will stand up in dispute or audit. For legal use, the stronger architecture is the one that links technical proof with documented operational controls and jurisdiction-specific admissibility requirements.
What industries benefit from blockchain document verification
Healthcare, legal services, education, financial compliance, and government all benefit because records frequently move between parties with different systems and different trust assumptions. The larger opportunity is not a single-chain pilot inside one organisation. It is interoperable verification across platforms, regulators, and regions, where document integrity, issuer trust, and revocation status must remain checkable even when the underlying networks differ.
Healthcare organisations, government agencies, legal technology companies, and enterprise software teams that need secure, scalable verification architecture can connect with Blocsys Technologies to discuss tamper-proof document verification systems, decentralised identity workflows, AI-assisted fraud controls, and cross-chain verification infrastructure for regulated environments.