Credential fraud is no longer a back-office nuisance. In India alone, educational certificate fraud affects over 20 million documents annually, and blockchain-based systems in large pilots have reduced verification time from weeks to under 5 seconds while achieving 99.8% fraud detection accuracy according to the IJERST study. For boards, CHROs, registrars, founders, and compliance leaders, that changes the conversation from document checking to trust infrastructure.
Tamper-Proof Digital Certificates: The Future of Academic & Employee Verificatio matters because verification now sits at the intersection of hiring speed, regulatory defensibility, cyber resilience, and cross-border mobility. A paper certificate can be forged. A central database can be altered, breached, or disputed. A cryptographically anchored credential changes the burden of proof.
For organisations evaluating blockchain certificate verification, enterprise credential verification platforms, or a digital verification solution for universities, the question isn’t whether the model is technically possible. It’s whether your operating model can absorb it cleanly, securely, and at scale. That’s where architecture decisions matter more than hype.
The same design logic also appears in adjacent security domains. Teams thinking about immutable trust records often benefit from studying how infrastructure leaders approach storage integrity and recovery, such as this ARPHost guide to ransomware-proof data. The principle is similar. Once trust data must survive tampering, immutability becomes a business requirement, not a technical preference.
For a deeper view of where this is heading in enterprise document workflows, Blocsys has also outlined how blockchain-based document verification prevents fraud in 2026.

Table of Contents
- The End of Forgery The Rise of Tamper-Proof Verification
- Why Traditional Verification Systems Fail Modern Needs
- How Blockchain Secures Digital Certificates
- Key Benefits for Universities and Enterprises
- Enterprise Use Cases and Implementation Patterns
- Integrating AI for Smarter Verification Systems
- How Blocsys Builds Secure Blockchain Verification Infrastructure
- Frequently Asked Questions
The End of Forgery The Rise of Tamper-Proof Verification
Why this moved from niche to infrastructure
The strongest signal in this market isn’t conceptual. It’s operational. Credly alone manages over 100 million credentials across more than 48 million individuals as noted in Edutech Global’s digital credentials analysis. That level of adoption shows credentialing has moved beyond experimentation into production-grade verification at institutional scale.
That matters for C-level buyers because scale answers a hard question. Can digital credentials support real verification workloads across employers, education providers, and compliance teams? The answer is increasingly yes, especially when open standards and tamper-proof verification are designed together.
Practical rule: If your verification model still depends on email chains, manual attestations, and point-in-time database lookups, you don’t have a trust system. You have an admin process.
The OECD observation cited in the same source is strategically important. Blockchain combined with open standards can help eliminate credential fraud and forgery. The technical takeaway isn’t just immutability. It’s interoperable trust.
Who needs to care now
Three groups have the most immediate stake.
- Universities and EdTech providers need a secure digital certification platform that graduates can share globally without repeated registrar intervention.
- Enterprise HR and compliance teams need HR document verification software that can stand up to audits, pre-employment checks, and licence tracking.
- Fintech, digital asset, and regulated businesses need verification records that are defensible, portable, and resistant to tampering.
For global organisations in Europe, the UK, the USA, the UAE, Singapore, Canada, Australia, and other cross-border hiring markets, the deeper implication is this: verification has become part of digital identity infrastructure. Once credentials must move between jurisdictions, employers, professional bodies, and software platforms, static files stop being enough.
Why Traditional Verification Systems Fail Modern Needs
Legacy workflows create silent exposure
Traditional verification systems fail because they were built to store documents, not to prove authenticity continuously. Paper certificates can be forged or altered. PDF copies can be edited. Even when an institution maintains a central database, external parties still depend on phone calls, emails, or manual portal checks to validate records.
That delay isn’t a minor inefficiency. It affects hiring velocity, onboarding certainty, and audit readiness. Teams often plug these gaps with process documents, templates, and exception handling. For example, many HR departments still rely on manual proofs such as these HR templates for employment verification letters when a trusted verification workflow would be more scalable.
A related issue is financial exposure. Indian enterprises face $1.2 billion in annual losses directly attributed to employee credential fraud, according to the Virtualbadge analysis. That’s the kind of risk category boards notice because it combines direct loss with reputational and compliance spillover.
Centralisation solves storage, not trust
Many organisations assume a central HRIS, SIS, or document repository solves the problem. It doesn’t. Central systems are useful systems of record, but they remain dependent on internal controls, administrator permissions, and perimeter security. They answer, “What do we currently store?” They don’t always answer, “Can an external verifier independently trust this artefact?”
In practice, secure document authentication fails as follows:
- Single points of failure mean one compromised database, account, or API can undermine confidence in the entire repository.
- Manual exception handling creates inconsistent decisions across departments, vendors, and geographies.
- Weak revocation discipline leaves expired or withdrawn qualifications circulating without a reliable verification state.
- Audit reconstruction becomes expensive because teams must piece together logs, emails, and approvals after the fact.
For organisations assessing the integrity side of document workflows, Blocsys has a useful explainer on what digital proof of document integrity means.
Central databases make documents accessible. They don’t automatically make them independently verifiable.
The result is a trust gap. Traditional systems optimise administration. Modern enterprises need verification infrastructure.
How Blockchain Secures Digital Certificates
Credential fraud succeeds when verification depends on trust in a document copy rather than proof of issuance, integrity, and status. Blockchain changes that control model by separating the credential file from the verification record and making the proof independently testable by any authorised party.
In practice, the certificate usually stays in an institutional portal, employee wallet, or document management system. The blockchain stores a cryptographic record of the credential’s contents, issuer identity, and issuance event. A verifier can then check whether the presented file matches the original record without requesting broad access to internal systems or relying on back-and-forth email confirmation.
The core mechanism is straightforward. A hashing function such as SHA-256 generates a unique fingerprint for the credential. If the file changes, even slightly, the fingerprint changes as well. The platform writes that fingerprint, along with selected metadata and issuer signatures, to an append-only ledger. Verification consists of recomputing the hash of the presented credential and comparing it with the registered on-chain value.
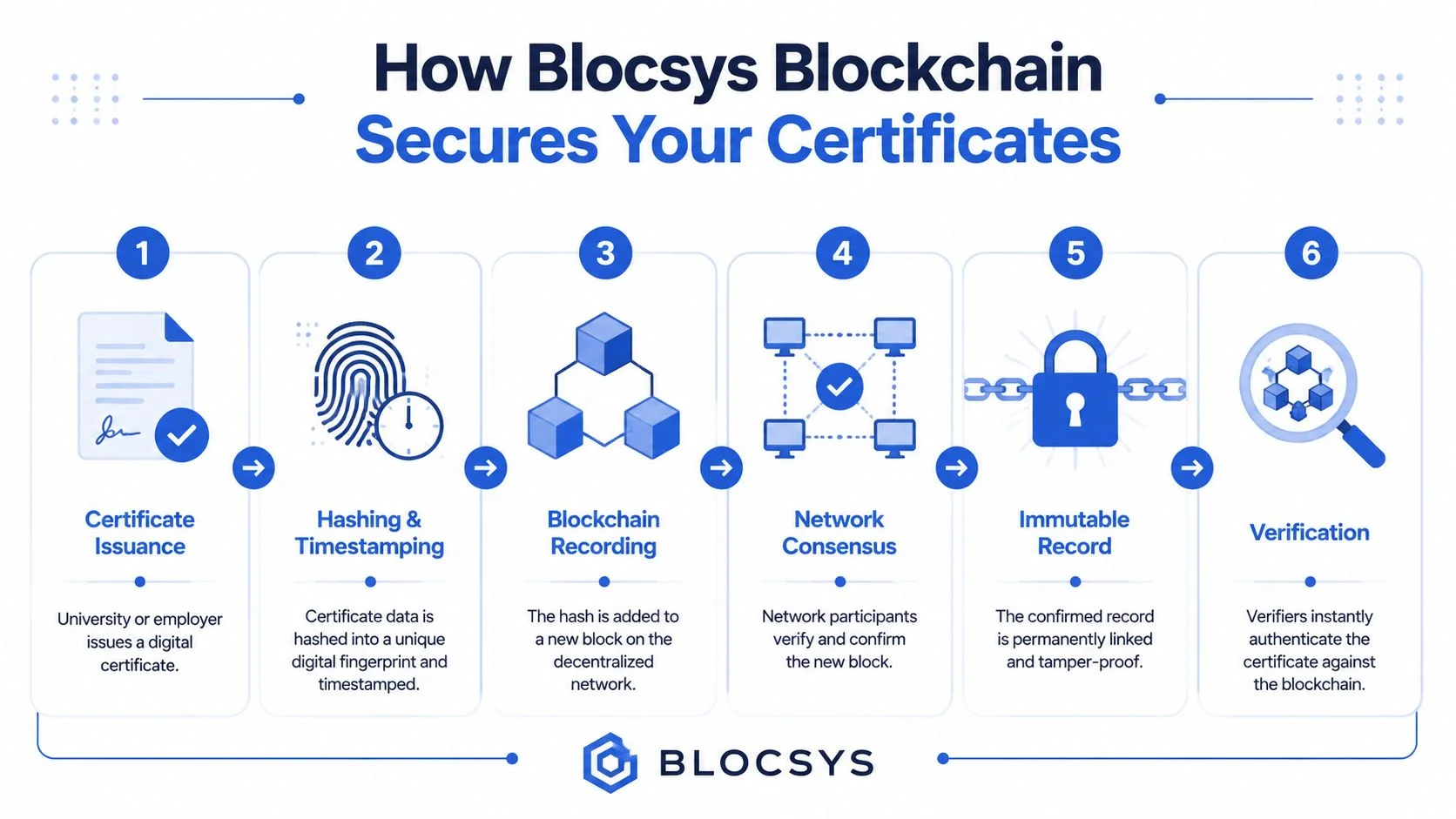
For enterprise buyers, the technical design matters less than the control outcomes it creates. Four design properties determine whether a blockchain credentialing system will hold up under audit, cross-border verification, and high-volume workforce operations:
- Integrity is machine-verifiable. The system can prove whether a certificate presented by a candidate, student, contractor, or employee is identical to the version originally issued.
- Issuer authenticity is tied to cryptographic keys. Trust shifts from manual registrar or HR confirmation to signature validation and key governance.
- Event history is time-stamped and reviewable. Issuance, renewal, update, and revocation actions form a traceable record that supports internal investigations and regulatory reviews.
- Verification is portable. Employers, licensing bodies, and partner institutions can validate credentials without connecting directly to the issuer’s production database.
That architecture has strategic implications for implementation. Enterprises should avoid storing full certificate payloads or personal data on-chain unless a legal review supports that model. In most regulated environments, the better pattern is to keep the document and sensitive attributes off-chain and place only the hash, schema reference, issuer signature, and status pointer on-chain. That approach reduces privacy exposure, supports data minimisation, and simplifies compliance with retention and deletion policies.
Teams that need a technical primer before selecting an architecture can review Blocsys’s explanation of blockchain technology and how it works.
Where smart contracts fit
Smart contracts add policy enforcement to the verification layer. They can govern who is allowed to issue credentials, which schemas are valid for a given programme or role, how expiration is handled, and what conditions trigger revocation or suspension. For enterprises, that turns blockchain from a passive evidence store into an automated control system.
This matters most in credentials with changing validity. Safety certifications expire. Professional licences can be suspended. Internal training credentials may lapse after a policy revision or failed recertification. A verification system that only proves historical issuance leaves a control gap. A system that checks current status at the same time is more useful for hiring, onboarding, vendor access, and compliance operations.
A practical evaluation framework is simple. Ask whether the platform can prove three things in one workflow: the credential was issued by an authorised entity, the file has not been altered, and the credential is still valid under current policy.
The investigation layer still matters. Background screening includes identity resolution, public records review, and document checks. For teams modernising those workflows, this guide on running a successful identity search is a useful companion because it shows how credential validation fits into a wider verification process.
Key Benefits for Universities and Enterprises
The value case in business terms
Verification delays still create measurable cost. Every manual check adds cycle time to admissions, hiring, contractor onboarding, and regulated role screening. Tamper-proof digital certificates improve that economics by reducing fraud exposure, shortening verification workflows, cutting registrar and HR administration, and making issuer trust easier to establish across borders.
For universities, the return shows up in fewer transcript requests, fewer manual confirmation emails, and less staff time spent answering routine authenticity queries. For enterprises, the return is broader. A single verification framework can support recruiting, internal mobility, supplier access, professional licence checks, and recurring compliance reviews without maintaining separate controls for each process.
The strategic advantage is standardisation. Once credential issuance, status, and revocation follow a machine-readable model, verification becomes an enterprise service rather than a series of one-off exceptions handled by different teams.
Traditional vs Blockchain Certificate Verification
| Feature | Traditional Verification (Paper/Centralized DB) | Blockchain-Based Verification |
|---|---|---|
| Security | Vulnerable to forgery, alteration, and unauthorised edits | Cryptographic proof makes tampering evident |
| Speed | Often depends on manual checks and institutional response times | Verification can be immediate once records are issued |
| Auditability | Fragmented logs across systems, emails, and teams | Time-stamped verification trail supports stronger audit evidence |
| Portability | Limited. Sharing often requires revalidation by issuer | Easier cross-border and cross-platform trust when standards are used |
| Revocation handling | Can be inconsistent or delayed | Can be governed through structured revocation logic |
| Operating model | Admin-heavy and staff-dependent | API-friendly and easier to automate at scale |
What boards should value most
Boards should assess these systems as control infrastructure, not as a narrow credentialing tool.
- Fraud containment lowers the risk of admitting unqualified applicants, hiring under false pretences, or granting system and site access to contractors with invalid certifications.
- Cycle-time reduction improves conversion in admissions and hiring because candidates, employees, and third parties spend less time waiting for document confirmation.
- Audit readiness improves when issuance, validation, and revocation records are time-stamped and easier to evidence during internal review or regulatory inspection.
- Cross-border interoperability matters for multinational employers and universities that need to assess credentials issued under different legal, educational, and technical standards.
- Operating efficiency improves because verification can be embedded into HRIS, ATS, student systems, vendor workflows, and access management through APIs rather than handled by email and phone.
One benefit is often missed. Governance becomes easier to scale.
A credential with a verified issuer, a clear schema, and a current validity state is easier to map to policy. That matters in sectors where compliance depends on proving that a person was qualified at a specific point in time, under a specific rule set. For a CIO or CHRO, that changes the decision framework. The question is no longer whether digital certificates look more modern than PDFs. The critical question is whether the organisation wants a verification process that remains manual and fragmented, or one that can be audited, integrated, and enforced consistently across business units and jurisdictions.
Enterprise Use Cases and Implementation Patterns
University issuance and graduate mobility
Academic issuance is the clearest use case because the pain is obvious. A graduate needs to prove an award. An employer needs confidence in its authenticity. The university wants to avoid endless manual validation requests.

A blockchain-based academic credential management platform changes that operating model. The institution issues a verifiable digital record. The graduate shares it directly. The employer or partner institution checks authenticity without chasing the registrar. For cross-border admissions, global recruitment, and digital-first alumni networks, that’s a structural improvement, not a cosmetic one.
The Nigerian case is instructive because it shows viability outside mature digital infrastructure environments. A blockchain-based digital certificate verification system built on Celo achieved an 82% security performance score and used QR-based instant authentication, according to the JETIA article. That matters for leaders in the UAE, Africa, South Asia, and multi-country education networks because it proves the model can address real infrastructure gaps, not just premium digital campuses.
Workforce compliance and regulated hiring
In enterprise settings, the use cases expand quickly:
- Pre-employment screening for academic records, licences, and certifications.
- Internal workforce compliance for roles that require ongoing credential validity.
- Contractor and partner onboarding where third-party qualifications must be trusted before system or site access.
- Regulated sectors such as fintech, digital assets, healthcare-adjacent services, and legal technology where weak credential assurance creates direct compliance exposure.
The implementation pattern that works best is usually not “put everything on-chain.” It’s “put proof, policy state, and verification logic on-chain.” That keeps the architecture disciplined.
A typical enterprise sequence looks like this:
- Choose the trust domain. Start with one credential family such as diplomas, employment records, or regulated certifications.
- Define issuer authority. Decide who can issue, update, suspend, or revoke.
- Anchor proof, not raw documents. Preserve hashes, signatures, timestamps, and status references.
- Expose verification through APIs and QR flows. Make validation simple for recruiters, auditors, and external partners.
- Integrate with existing systems. Treat HRIS, ATS, SIS, and compliance tools as workflow systems, not the root of trust.
This walkthrough helps visualise how these systems are introduced in practice:
A practical rollout pattern
The strongest enterprise programmes usually start narrowly. They don’t attempt to rebuild identity from scratch. They solve one expensive verification problem first, then expand.
Start with the credential that creates the most operational delay or legal exposure. Don’t start with the one that looks easiest in a demo.
That’s especially relevant for enterprises operating across Europe, the UK, the USA, Singapore, and the UAE, where cross-border certificate verification often involves multiple employers, regulators, and educational systems. In those environments, the value comes from interoperability and governance discipline, not just from blockchain adoption itself.
Integrating AI for Smarter Verification Systems
AI improves the control layer
Blockchain proves authenticity. AI improves decision quality around the verification process. That distinction matters because many organisations blur the two and end up with unclear architecture.
In an enterprise credential verification platform, AI is most useful in the surrounding control layer. It can classify incoming credential types, extract fields from semi-structured records, flag anomalies in submission patterns, and route exceptions to the right reviewer. The blockchain remains the trust anchor. AI becomes the operational intelligence layer.
For teams thinking about these combined architectures, Blocsys has written about AI and blockchain integration in 2026.
Where leaders should apply AI first
The highest-value AI use cases tend to be selective rather than broad.
- Document interpretation helps standardise messy inbound records before they’re normalised into a verifiable format.
- Anomaly detection can identify suspicious issuance or verification patterns that merit further investigation.
- Skills and role matching can connect already-verified qualifications to internal mobility or hiring workflows.
- Operational triage can separate straight-through verification from cases that need manual review.
This creates a stronger business case than security alone. A company doesn’t just reduce fraud risk. It also builds a smarter workforce verification platform that supports talent operations, compliance teams, and identity-led onboarding.
The architectural discipline is simple. Let AI recommend, classify, and prioritise. Let cryptographic verification prove.
How Blocsys Builds Secure Blockchain Verification Infrastructure
What enterprise delivery actually requires
Most verification programmes fail at the implementation layer, not the concept layer. The hard part is connecting trust, workflow, privacy, and governance without creating another isolated tool.
Blocsys operates in that implementation space as a blockchain and AI infrastructure engineering company. For organisations building tamper-proof certificate systems, the company’s document verification approach uses deterministic hashing and blockchain anchoring to create independently verifiable proof, while keeping storage and workflow concerns separated. That design choice matters because enterprise-grade verification should minimise data exposure while preserving auditability.
Execution typically requires four capabilities: blockchain architecture, smart contract design, system integration, and operational controls. Buyers evaluating partners should look for experience in permissioning, issuer key management, revocation logic, API design, and integration with existing enterprise systems rather than only front-end credential issuance.
For teams mapping vendor selection and programme design, this Blocsys blockchain consulting partner guide for 2026 is a useful starting point. Organisations that need broader build support can also review Blocsys’s Blockchain Development Company services and the company’s home page for its wider enterprise blockchain and AI delivery focus.
The right engagement model is usually phased. Start with one credential family, one verification workflow, and one governance policy. Then expand to cross-border certificate verification, workforce compliance systems, and broader digital identity authentication use cases once the trust model is proven internally.
Frequently Asked Questions
Are blockchain-based certificates legally usable in enterprise workflows
They can be, but legal usability depends on jurisdiction, sector rules, issuer authority, and how the credential is governed. In practice, most organisations use blockchain-based certificates as a stronger verification mechanism inside existing legal and compliance processes, rather than as a standalone legal substitute for every document category.
How is privacy protected if blockchain is involved
Well-designed systems don’t place sensitive personal data directly on a public ledger. They anchor cryptographic proof, signatures, timestamps, and status references while keeping the underlying document in controlled storage or user-held delivery flows. That approach supports verification without unnecessary data exposure.
Can this integrate with existing HR and student systems
Yes, if the platform is architected as verification infrastructure rather than as a replacement for HRIS or SIS tools. Most successful deployments connect issuance, verification, and revocation to existing systems through APIs, event triggers, and policy controls.
What determines ROI in a verification programme
ROI usually comes from fewer manual checks, faster onboarding, lower fraud exposure, cleaner audit trails, and less dependency on fragmented verification vendors or internal admin teams. The strongest returns appear where verification is frequent, regulated, cross-border, or operationally slow.
If your organisation is evaluating tamper-proof certificate infrastructure, Blocsys Technologies can help assess the right architecture, governance model, and implementation path for academic verification, employee credentialing, and enterprise-grade blockchain verification systems. Connect with the team to discuss a practical rollout aligned to your compliance, security, and integration requirements.