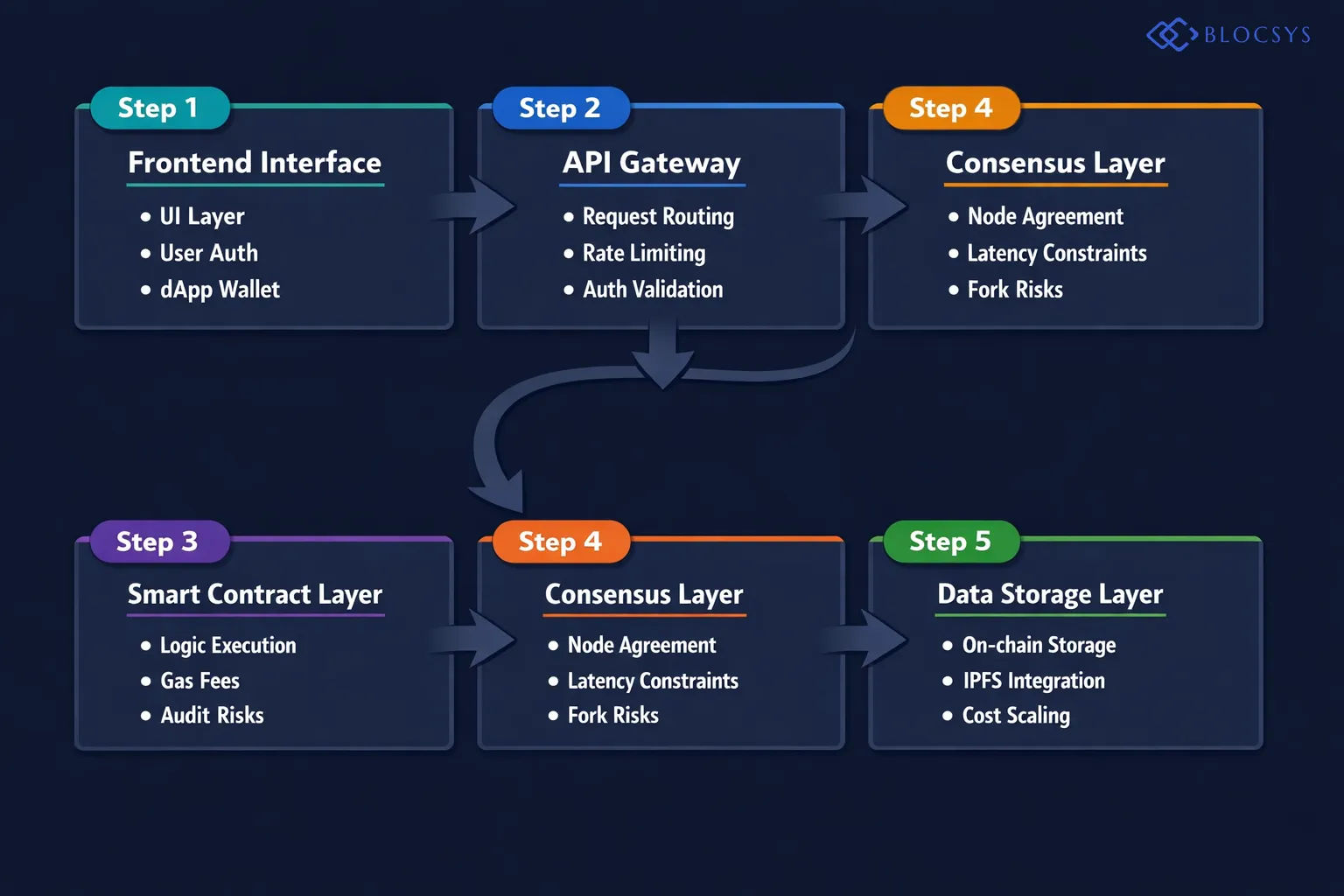
Building a successful Web3 company demands far more than a compelling whitepaper or a bold tokenomics model. Founders quickly discover that web3 business challenges run far deeper than market positioning or product-market fit. From crippling throughput bottlenecks to catastrophic smart contract exploits that erase user trust overnight, these obstacles derail even well-funded teams with experienced engineers. Understanding these challenges before deploying a single line of production code is critical. Our Blockchain Development services exist precisely to help startups navigate this complex and high-stakes terrain. For a broader strategic perspective, the Crypto & Blockchain Startup Challenges: The Complete Founder’s Guide to Building in Web3 (2026) covers every dimension founders face today — including funding, talent, regulation, and beyond.
Core Web3 Business Challenges in 2026
The Web3 ecosystem evolves at a relentless pace. New chains emerge weekly, protocols upgrade without warning, and developer tooling shifts constantly. Consequently, startups must build on infrastructure that can change beneath their feet. Three challenges consistently prove most disruptive for early-stage teams: scalability, security, and smart contract reliability.
However, in 2026, two additional pressures have intensified significantly. Regulatory compliance now shapes architecture decisions from day one. The growing sophistication of on-chain attackers demands a more structured and continuous security posture than most early teams anticipate. Understanding each challenge helps founders allocate engineering resources wisely and avoid the costly mistakes that sink otherwise promising projects.
Why Technical Debt Hits Web3 Harder
In traditional software, technical debt accumulates slowly. Teams address it incrementally across sprint cycles. In Web3, however, a single architectural mistake can mean millions of dollars lost in one exploit — or a forced chain migration that alienates your entire user base. Moreover, decentralized systems are inherently harder to patch quickly.
A bug in a deployed smart contract cannot always be fixed with a simple update push. Therefore, getting your architecture right from the very beginning matters enormously — far more than it does in conventional software development. The cost of getting it wrong is not a sprint delay. It is an irreversible loss of funds and reputation.
Blockchain Scalability Problems: The Growth Killer
Blockchain scalability problems are among the most well-documented issues in the industry. Most public blockchains process a fraction of the transactions that traditional payment networks handle effortlessly. Ethereum processes roughly 15 to 30 transactions per second at base layer. By contrast, Visa handles thousands per second. This gap creates real-world friction for startups trying to onboard mainstream users and support consumer-grade interaction volumes.
Layer 2 and Cross-Chain Scaling Solutions
Web3 scalability solutions have matured substantially entering 2026. Layer 2 rollups — including Optimistic Rollups like Optimism and Arbitrum, and zero-knowledge rollups like zkSync and Starknet — now process millions of transactions daily at a fraction of mainnet costs. Additionally, state channels and validiums offer further options for high-frequency transaction use cases. Each approach trades finality speed, decentralization, or developer complexity in different ways.
Furthermore, cross-chain interoperability has become a strategic priority for growth-stage protocols. Fragmented liquidity across Layer 2 networks creates compounding user experience challenges. Users must bridge assets, pay fees on multiple chains, and manage several wallets simultaneously. Therefore, startups building DeFi or gaming products need a clear cross-chain strategy from day one. The Telegram Mini App — Web3 Gaming and DeFi Platform demonstrates how thoughtful architecture handles cross-chain complexity while still delivering smooth user experiences.
However, bridge infrastructure introduces serious security risks. Bridge exploits have cost the industry billions of dollars since 2021. Consequently, selecting and auditing bridge infrastructure deserves the same rigor as auditing your core protocol contracts. Never treat bridges as trusted black boxes.
Choosing the Right Blockchain for Your Use Case
Not every startup needs Ethereum mainnet. Permissioned blockchains suit enterprise supply chain applications requiring privacy and controlled access. Public chains suit open DeFi protocols benefiting from composability. Hybrid models suit startups needing compliance alongside decentralization. Consequently, the best chain depends entirely on your product’s specific requirements.
Matching your blockchain choice to your throughput, cost, and compliance needs dramatically reduces scalability pain later. Our Blockchain Supply Chain Traceability System for Manufacturing illustrates how the right chain selection powers industrial-grade performance at scale without sacrificing data integrity or auditability.
“Most scalability failures in Web3 startups stem not from the blockchain itself, but from founders selecting the wrong chain for their actual transaction volume requirements. You must stress-test your architecture at ten times your expected peak load before writing a single line of production smart contract code.” — Senior Blockchain Architect, Web3 Infrastructure Firm

Smart Contract Security Risks Every Founder Must Address
Smart contract security risks represent perhaps the single greatest technical threat to Web3 startups today. Billions of dollars have drained through smart contract exploits since 2020. Reentrancy attacks, integer overflows, access control flaws, and oracle manipulation all feature regularly in devastating post-mortems. Founders must treat smart contract security as a first-class engineering concern — not an afterthought bolted on before launch.
Most Common Smart Contract Vulnerabilities
Reentrancy attacks allow malicious contracts to repeatedly call a vulnerable function before the first execution completes. This exploit famously drained The DAO in 2016 and, remarkably, continues to appear in fresh audits today. Additionally, improper access controls let unauthorized wallet addresses execute privileged admin functions. Moreover, logic errors in token economics — such as unchecked minting functions or faulty reward distribution calculations — can instantly destroy a protocol’s entire value.
Flash loan attacks, which exploit price oracle manipulation within a single transaction block, grew dramatically between 2023 and 2025. Attackers borrow enormous capital, distort on-chain price feeds, drain liquidity pools, and repay the loan in a single atomic transaction. Therefore, developers must understand these attack vectors deeply before deploying any contract that holds real user funds.
Real-World Case Studies: Exploits That Ended Promising Projects
Several high-profile failures illustrate what is genuinely at stake. The Ronin Network exploit drained over $600 million through compromised validator keys — a failure of infrastructure security, not contract code. The Euler Finance hack drained $197 million through a logic flaw in donation and liquidation mechanics that slipped past multiple audits. Furthermore, the Mango Markets exploit leveraged oracle price manipulation to drain $117 million in a single transaction sequence.
Each of these incidents shares a common thread. Teams underestimated attack surface complexity. Additionally, most of these projects had completed at least one formal audit before the exploit. Therefore, auditing is necessary — but never sufficient on its own. Security requires continuous, multi-layered effort across your entire development lifecycle.
Smart Contract Audit Process: What Founders Need to Know
The smart contract audit process intimidates many founders, particularly those without a security engineering background. However, understanding what an audit involves — and what it cannot catch — dramatically improves your overall security posture. Audits provide a structured, expert review of your codebase at a specific point in time. They do not provide a permanent certificate of security.
Smart Contract Audit Checklist
A thorough smart contract audit checklist covers the following critical areas:
- Access control review: Verify that only authorized addresses can call privileged and administrative functions.
- Reentrancy analysis: Check all external calls for reentrancy vulnerabilities, especially in withdraw and transfer logic.
- Integer arithmetic: Confirm overflow and underflow protections are in place across all mathematical operations.
- Oracle dependency review: Assess whether price feeds can be manipulated within a single transaction block.
- Upgrade mechanism review: Confirm proxy patterns and upgrade logic are correctly implemented and access-controlled.
- Business logic validation: Verify that tokenomics, reward mechanics, and economic assumptions behave correctly under adversarial conditions.
- Denial-of-service vectors: Identify functions that attackers could block or make unusably expensive through crafted inputs.
Before engaging an external auditor, run automated static analysis tools internally. Tools like Slither, MythX, and Aderyn catch common vulnerability patterns and integrate directly into CI/CD pipelines. Additionally, conducting thorough invariant and fuzz testing before the audit maximises the auditor’s time on complex business logic — the area where automated tools consistently fall short.
How to Choose an Auditor and What It Costs
Choosing the right auditor matters as much as getting an audit at all. Reputable firms include Trail of Bits, OpenZeppelin, Halborn, Certik, and Consensys Diligence. Each carries different specialisations, availability windows, and pricing structures. A thorough audit from a reputable firm typically ranges from $10,000 to $50,000 for moderately complex contracts.
Large DeFi protocols with multiple interacting contracts and complex economic mechanisms can cost significantly more — sometimes exceeding $200,000 for comprehensive engagements. Moreover, lead times at top-tier firms frequently run six to twelve weeks. Therefore, budget time and money for auditing early in your development roadmap, not two weeks before your planned launch date. Our Premium Guide: Decentralized Exchange (DEX) Security 2026 Strategy provides a comprehensive security framework specifically for DeFi protocols.

Bug Bounty Programs and Vulnerability Disclosure in Web3
Bug bounty programs web3 have become an essential layer of blockchain startup security. Formal audits provide a point-in-time assessment of your codebase. Bug bounties provide continuous, community-driven scrutiny after launch. Together, they form a defense-in-depth security strategy that sophisticated attackers find significantly harder to defeat.
Immunefi and the Solana Ecosystem
Immunefi has emerged as the leading bug bounty platform for Web3 protocols. It hosts programs for some of the largest DeFi protocols in the industry, with total bounty payouts exceeding $100 million across its platform history. Researchers earn rewards proportional to the severity of vulnerabilities they discover. Critical vulnerabilities enabling complete protocol drain typically command bounties ranging from $50,000 to several million dollars.
The Solana ecosystem has developed its own active bug bounty infrastructure. Solana’s official security program covers the core protocol directly. Additionally, major Solana-based DeFi protocols run independent programs on Immunefi and other platforms. Furthermore, the Solana Foundation actively funds security research and developer education, making the ecosystem particularly well-resourced for security-focused builders entering the space in 2026.
Setting Up Your Own Bug Bounty Program
Launching a bug bounty program signals maturity and seriousness to your community and to potential investors. To launch effectively, define clear scope boundaries first. Specify which contracts and interfaces are in scope and which are explicitly excluded. Additionally, publish clear severity tiers with corresponding reward ranges. Researchers will not invest time in programs with vague or ungenerous reward structures.
Moreover, establish a responsible disclosure policy committing to timely acknowledgment and remediation timelines. Researchers value clear communication as much as financial rewards. Therefore, an accessible and responsive triage process dramatically increases the quality and quantity of reports your program receives. Even startups with modest budgets benefit significantly from running structured programs at lower reward tiers.
Smart Contract Security Best Practices 2026
Smart contract security best practices 2026 have evolved substantially as the threat landscape has matured. Several practices now reflect industry consensus for production deployments and deserve priority attention from every founding team.
Firstly, adopt a multi-layered testing strategy. Combine automated static analysis with comprehensive unit tests, invariant tests, and fuzz testing. Invariant testing — where developers define properties that must always hold regardless of input — has gained strong adoption as a powerful complement to standard unit test suites. Additionally, run economic attack simulations on testnets before any mainnet deployment. Specifically, test flash loan scenarios, oracle manipulation attacks, and large liquidity withdrawal events.
Secondly, implement circuit breakers and emergency pause mechanisms. Protocols should be able to pause operations within minutes of detecting anomalous on-chain activity. However, pause mechanisms must themselves be securely implemented and access-controlled. Furthermore, separate upgrade authority from operational authority. Use timelocks on governance decisions and major contract upgrades. A 48-hour or 72-hour timelock gives your community time to review changes and exit positions if necessary.
Thirdly, monitor on-chain activity continuously post-launch. Tools like Forta, OpenZeppelin Defender, and Tenderly allow teams to configure real-time alerts for suspicious transaction patterns. Additionally, establish a clear incident response playbook before you need it — not during an active exploit when every minute of delay costs real user funds. Therefore, combining all these layers significantly reduces the residual risk that reaches and remains in production.
“The weakest point in most Web3 startups is never the audited smart contract — it is the three unreviewed JavaScript dependencies sitting quietly in their front-end build pipeline. Sophisticated attackers know this precisely. Your security posture is only as strong as your entire stack, not just the on-chain code.” — Web3 Security Researcher, Decentralized Protocol Auditing Firm
Crypto Startup Security Challenges Beyond the Smart Contract
Crypto startup security challenges extend well beyond the smart contract layer. Infrastructure security, private key management, and front-end vulnerabilities all deserve equal engineering attention. Many high-profile hacks in 2024 and 2025 targeted front-end interfaces rather than on-chain contracts. Attackers replaced legitimate wallet addresses in the UI, silently redirecting user funds to attacker-controlled wallets. Consequently, a perfectly audited smart contract cannot protect users if the interface delivering it is compromised.
Private Key and Wallet Infrastructure Security
Private key management is the most critical operational security challenge in the entire Web3 stack. Hot wallets connected to the internet remain perpetually vulnerable to compromise. Hardware security modules and multi-signature wallet schemes dramatically reduce this risk by requiring multiple independent approvals before funds move. Moreover, multi-party computation wallets distribute signing authority across multiple independent parties, eliminating dangerous single points of failure entirely.
Startups handling institutional funds should also consider regulatory custody requirements carefully. The Blockchain Startup Regulatory Challenges: A Practical Compliance Roadmap for 2026 covers custody compliance frameworks in thorough detail, including jurisdiction-specific requirements that increasingly affect product architecture decisions.
Front-End and API Attack Surfaces
DNS hijacking, compromised npm packages, and malicious browser extensions all create serious front-end attack vectors that many Web3 teams chronically underestimate. Therefore, startups must implement subresource integrity checks, strict content security policies, and regular dependency audits as baseline hygiene. Additionally, API endpoints interacting with blockchain nodes must authenticate requests rigorously and validate all inputs without exception.
Rate limiting and anomaly detection reduce exposure to bot-driven attacks significantly. Furthermore, incident response playbooks should address Web3-specific scenarios — including procedures for pausing or upgrading contracts under emergency conditions when every minute directly impacts user fund safety. Teams that rehearse these scenarios before launch respond far more effectively when real incidents occur.
Regulatory and Compliance Risks as a Web3 Business Challenge
Regulatory and compliance risk has rapidly become one of the most significant web3 business challenges founders face in 2026. The global regulatory landscape for crypto and blockchain businesses has shifted dramatically. The EU’s MiCA regulation has introduced formal licensing requirements across Europe. US enforcement activity has intensified, targeting DeFi protocols, stablecoin issuers, and token offering platforms with increasing frequency and severity.
Founders must now treat compliance as an engineering requirement — not a legal afterthought addressed after product launch. Smart contract design choices carry direct regulatory implications. For example, whether a protocol can freeze or reverse transactions affects its classification under various regulatory frameworks. Token classification decisions trigger securities law obligations in multiple jurisdictions simultaneously.
Furthermore, KYC and AML requirements now apply to an expanding range of Web3 services. Teams building products with fiat on-ramps, institutional clients, or regulated asset classes must architect compliance infrastructure from day one. Retrofitting compliance onto a deployed protocol is technically complex, expensive, and occasionally impossible without a full redeploy. Therefore, engaging legal counsel with specific Web3 expertise early in your build — ideally before finalising your architecture — pays significant long-term dividends.
Building a Resilient Technical Foundation for Web3 Growth
Addressing web3 business challenges requires a systematic, layered approach across every part of your stack. Scalability, security, smart contract reliability, and compliance are not independent problems — they interact and amplify each other. A scalability solution relying on an untested bridge introduces new attack surface. A security shortcut skipping formal verification trades short-term development speed for long-term catastrophe.
Moreover, your team’s ability to attract and retain skilled blockchain engineers directly shapes your technical resilience over time. The Blockchain Startup Talent Challenges: How to Build and Retain a World-Class Web3 Team in 2026 explores practical strategies for building the engineering talent base your protocol needs to execute safely at scale.
Furthermore, user trust ties directly to your public technical reputation. Startups that suffer avoidable exploits rarely recover their community’s confidence, regardless of how much they raise afterward. By contrast, teams that demonstrate transparency, rigorous auditing, and proactive security communication build durable and defensible brands. Our Crypto Startup Market Challenges: Overcoming User Adoption and Trust Barriers in Web3 (2026) explores precisely how technical credibility translates into measurable user acquisition and long-term retention advantages.
Ultimately, the Blockchain Development expertise required to build safely at scale in Web3 is not a commodity — it is a genuine strategic differentiator. Investors increasingly scrutinise technical architecture and security posture during due diligence. Therefore, solving these challenges early strengthens your fundraising position considerably. The Crypto & Blockchain Startup Challenges: The Complete Founder’s Guide to Building in Web3 (2026) ties all these strategic and technical threads together for founders who want the complete picture.
Frequently Asked Questions
Here are direct answers to the questions founders ask most often about web3 business challenges and technical risk management.
What are the biggest web3 business challenges for startups in 2026?
The five most critical challenges are blockchain scalability, smart contract security, infrastructure security, regulatory compliance, and developer talent acquisition. Scalability limits how many users your product can serve before fees spike and performance degrades. Smart contract vulnerabilities expose your protocol to potentially catastrophic and irreversible financial loss. Infrastructure security determines whether attackers can bypass on-chain protections entirely. Compliance requirements now shape architecture decisions from the very first sprint. Addressing all five systematically from the start costs far less than retrofitting after you have real users and real funds at risk.
How do blockchain scalability problems affect Web3 startups specifically?
High gas fees and slow transaction finality directly damage user experience in measurable ways. When network congestion spikes, transaction costs can exceed the actual value of small transactions entirely, effectively excluding retail users and making microtransaction use cases economically unviable. Layer 2 web3 scalability solutions mitigate many of these issues, but they introduce bridging complexity and fragmented liquidity that compounds UX challenges. Startups must design their product architecture around specific throughput and latency requirements rather than defaulting reflexively to the most popular chain without validating fit.
What should a smart contract audit checklist include?
A thorough smart contract audit checklist must cover access control review, reentrancy analysis, integer arithmetic protections, oracle dependency assessment, upgrade mechanism review, business logic validation, and denial-of-service vector identification. Beyond the checklist itself, teams should run automated static analysis with tools like Slither, conduct invariant and fuzz testing, and simulate economic attack scenarios on testnets before engaging external auditors. Auditors use their time most effectively when your internal testing has already resolved common, lower-complexity vulnerabilities, allowing them to focus on the subtle business logic flaws that automated tools consistently miss.
How do bug bounty programs work for Web3 startups?
Bug bounty programs web3 invite independent security researchers to probe your live protocol for vulnerabilities in exchange for structured financial rewards. Platforms like Immunefi host your program, manage researcher submissions, and facilitate payouts. You define the scope, severity tiers, and reward ranges. Researchers earn bounties proportional to the severity of their findings — critical vulnerabilities enabling full protocol drain can command rewards in the millions for major protocols. Bug bounties complement formal audits by providing continuous scrutiny that a point-in-time audit cannot offer and that scales with your protocol’s growth and total value locked.
How can Web3 startups manage crypto startup security challenges on a limited budget?
Prioritise auditing your highest-risk contracts first — specifically those holding the most user funds or controlling administrative functions. Integrate free open-source static analysis tools like Slither directly into your CI/CD pipeline so every code push receives automated scanning. Implement multi-signature controls on all admin wallet addresses from day one, before any funds enter the system. Launch a structured bug bounty program on Immunefi even at modest reward levels — researcher attention delivers real value at any budget tier. Additionally, engage Web3 legal counsel early to avoid compliance architecture mistakes that prove far more expensive to correct after deployment than before it.
Ready to move beyond theory and build an intelligent platform that delivers real-world value? Blocsys Technologies specialises in engineering enterprise-grade AI and blockchain solutions for the fintech, Web3, and digital asset sectors. Connect with our experts today to discuss your vision and chart a clear path from concept to a secure, scalable reality.